I posted my password / API key on GitHub
Or GitLab, or any other public source control management platform. Now what?
I stumbled on a website that continuously scans GitHub, GitLab and BitBucket, the 3 most common places to host source code publicly, and shows you committed SSH passwords, API keys for common services, databases and so on.
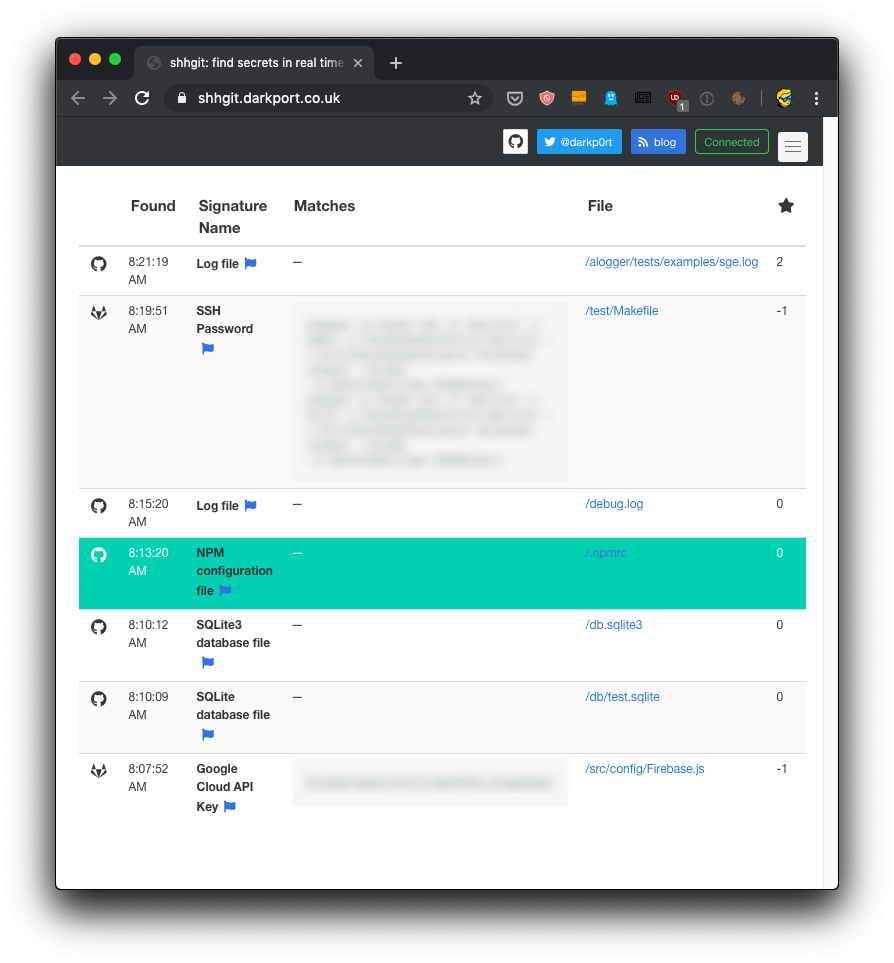
It’s scary, right?
Raise your hand if it never happened to you. We can make mistakes. And when this happens, there’s no other way than quickly invalidating the password or API key that was exposed to the public.
For people new to Git: you can’t just rollback the commit, because it will still be kept in the history of the repository.
Your reputation, the reputation of your project, the security of your users is at stake.
After you fix the emergency, the issue is: how to prevent the problem? What’s the answer? What’s the solution that can help us avoid commit secrets to a publicly available Git repository?
The answer is: workflow and tooling.
First, never add your API keys or passwords inside source code. They can hide in there, quietly. Instead, always add them to a .env file in the project root folder, and add .env to your .gitignore file, so it will never be committed. Use a tool like dotenv to access them.
Use git-secrets, a tool that will help you avoid committing secrets to Git.
In macOS you install it using Homebrew:
brew install git-secrets
then go inside the repository you want to activate it on, and run
git secrets --install
to install the Git pre-commit hook. This will ensure the tool runs before Git makes the commit to the repo.
If you use Amazon Web Services (AWS), run this command to add the set of patterns used by that services credentials:
git secrets --register-aws
You can immediately scan for issues using
git secrets --scan
Ideally the tool should not print anything. But if you have issues, it will give you plenty of details.
→ I wrote 17 books to help you become a better developer:
- C Handbook
- Command Line Handbook
- CSS Handbook
- Express Handbook
- Git Cheat Sheet
- Go Handbook
- HTML Handbook
- JS Handbook
- Laravel Handbook
- Next.js Handbook
- Node.js Handbook
- PHP Handbook
- Python Handbook
- React Handbook
- SQL Handbook
- Svelte Handbook
- Swift Handbook
Also, JOIN MY CODING BOOTCAMP, an amazing cohort course that will be a huge step up in your coding career - covering React, Next.js - next edition February 2025